MOVEit Transfer mass extortion (2023)
May–December 2023What Happened
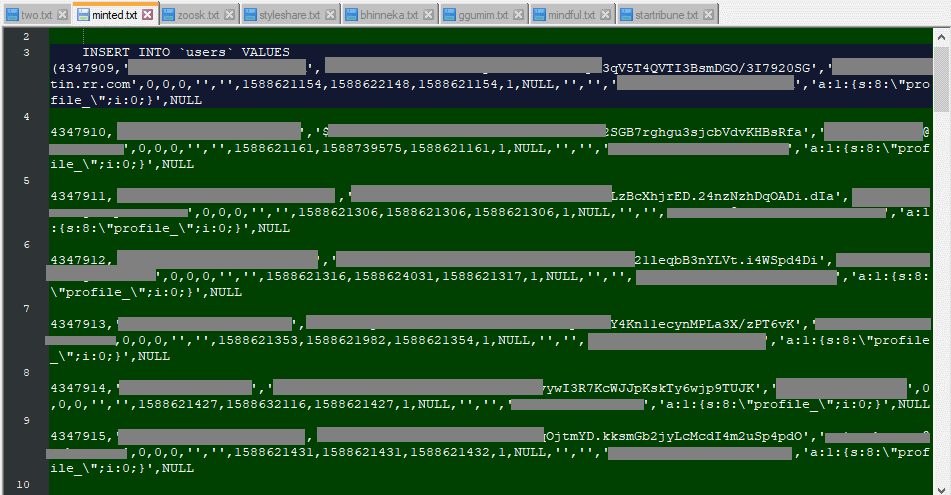
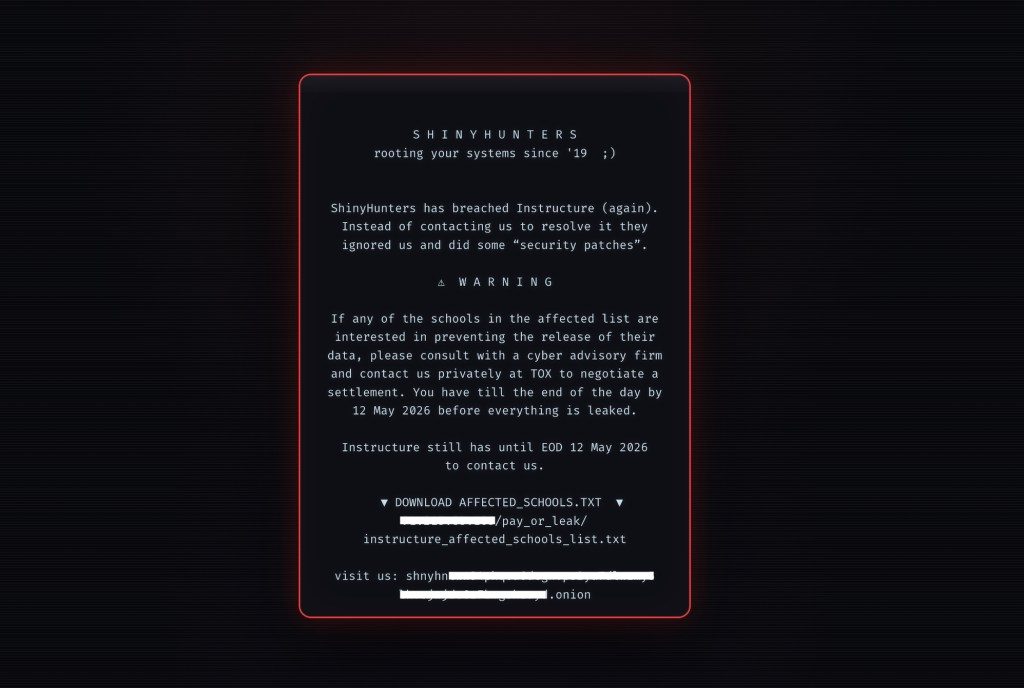
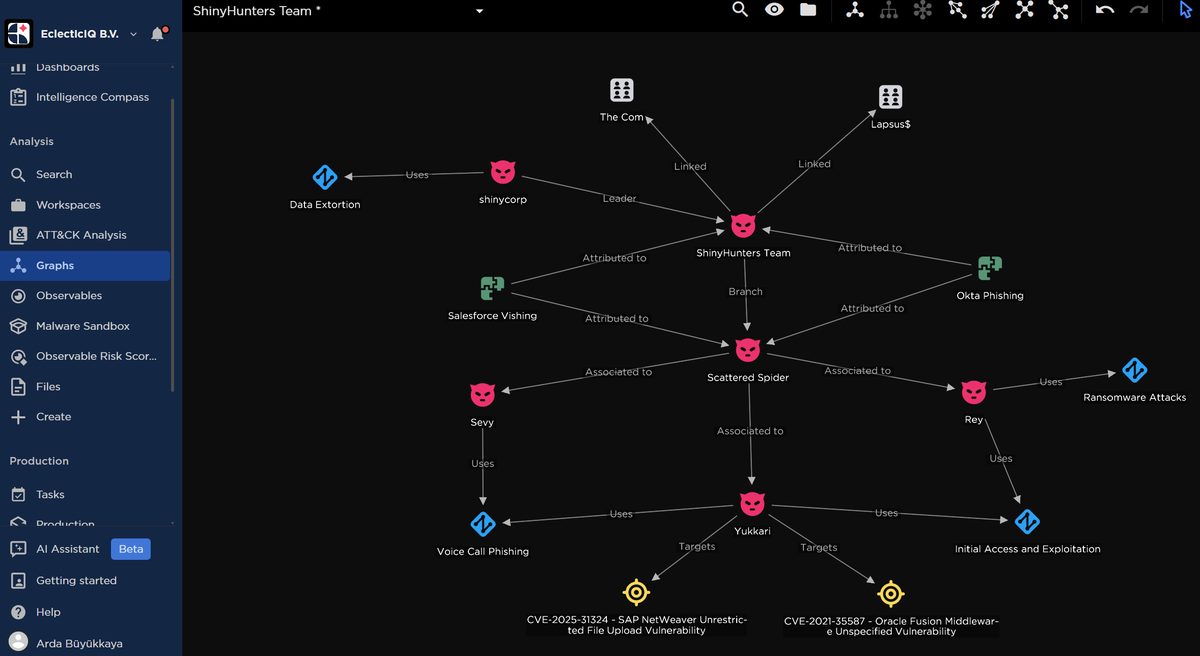
The Cl0p ransomware group exploited a zero-day in Progress Software's MOVEit file-transfer tool, stealing data from roughly 2,700 organizations and tens of millions of individuals, including state DMVs, U.S. federal agencies, and the BBC. Cl0p named victims on its leak site one by one and demanded payment within days.
Outcome
Most victims refused to pay. Cl0p released stolen data in waves through late 2023, fueling years of identity-theft litigation.
MOVEit became the reference case for vendor-driven mass breaches, pushing regulators and insurers to focus on third-party software supply chains.
Why It's Relevant Today
Like Instructure, Progress was a single vendor whose product sat inside thousands of customer environments, turning one bug into a sector-wide event. The Canvas incident is following the same pattern in education.